Spyse is a new cybersecurity search engine for collecting mass technical data about internet assets. Spyse team has recently combined all their products into one, offering a wide plethora of possibilities for conducting cyber reconnaissance and data gathering.
With a primary focus on productivity, Spyse allows seeking through one of the largest technical database, which lets users not only obtain needed information but explore relationships between the internet objects.
Data Collection
Security experts are usually one step behind hackers in the cybersecurity race. In efforts to turn the tables, Spyse has implemented a system in which users gain access to readily-collected data. This is done in hopes to speed up the time in which vulnerabilities can be sealed and protective measures implemented.
Over ten self-developed scanners are implemented by Spyse to parse the web regularly, gathering data from multiple resources. Gathered data is compared with other sources and processed by Spyse personnel to establish authenticity, and create a fluid browsing experience, showing all relationships between found data.
There are several productivity benefits of using the Spyse search engine. This service implements a distribution system consisting of fifty servers located around the world, which lets them scan regularly, bypassing location scanning restrictions, and ISP blocking. Continuous unrestricted scanning lets Spyse keep the database fresh.

How Spyse Maintains Its Database?
Database access is a key benefit for all Spyse users. It removes the tedious work of performing manual scans and establishing relationships between newfound data.
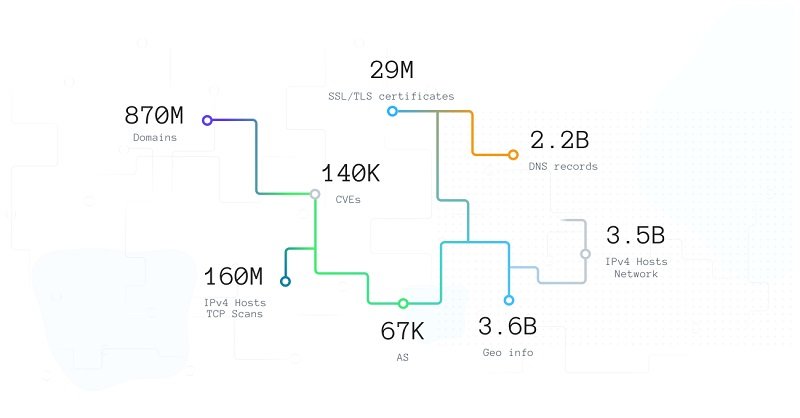
Spyse employs fifty highly productive, fast, and reliable servers dedicated to storing hot data. The data is analyzed and connected, letting users visualize a full picture of their network (or anyone else’s). The database is a cluster from these servers, storing seven billion documents broken up into 250+ shards which make up for over five terabytes of data. Due to uninterrupted scans, this data is constantly being expanded and updated.
A user with this database at their disposal, can map infrastructures at a very advanced pace, track malicious behavior on their servers, and overall automate complex processes which used to be extremely limited and time-consuming.
Using Spyse API and Website
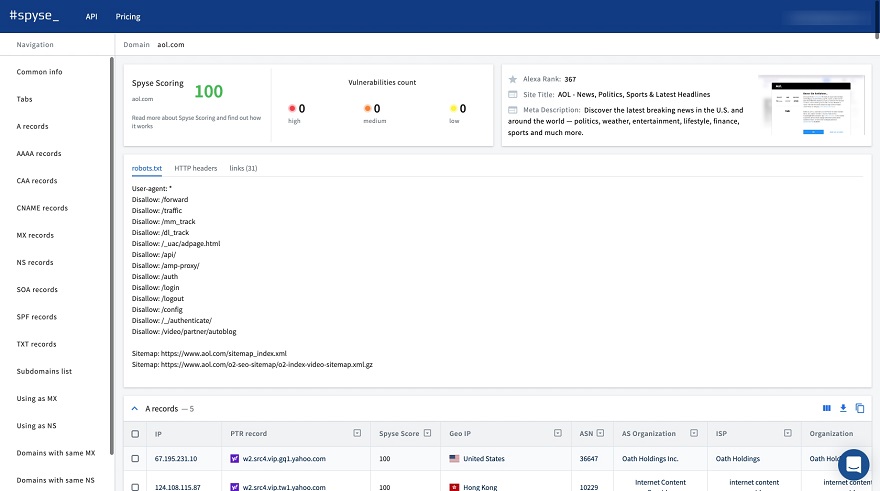
The data presentation on Spyse is very straightforward, and data can be attained both from their web service, and the API.
On the website, users will find a customizable and dynamic web interface, offering lots of productivity perks. For instance, users receive data in tables which they can then move around and customize. The data can be filtered so that only relevant results are visible and there’s no need to analyze large data sets. Additionally, everything found using a search engine can be downloaded for offline access.
Another great way to collect data is by using the Spyse API. With expanded documentation made on Swagger, the API offers lots of flexibility and can be easily integrated into different tools and services. A great alternative while the team is still working on their CLI. Additionally, the team offers a well-made Python wrapper made by outsourced developer zer0pwn.
If none of the above suits you, you can use Spyse’s python wrapper which was designed by outsourced developer Zer0pwn, who is well revered among pen testers.
Advanced Search and Security Scoring
Spyse has two neat tools that further simplify the quest for data: Advanced Search and Security Scoring.
Advanced search is like a live filter where users can apply up to 5 search parameters to a single query. This greatly narrows down data so that users don’t need to dig through heaps of information to find what they’re looking for. For example: applying just 3 parameters can help find all subdomains of some company, define vulnerabilities related to those subdomains, and show connections with other companies or network elements to get a much broader vision.

The Security Scoring tool quickly analyzes networks or infrastructures as a whole, searching for vulnerabilities inside. The tool takes all information from Spyse scanners and connects it to the CVE, providing an overall security rating for a network or infrastructure ranging from 0-100. Users are presented with an overall security assessment, and they can explore every found vulnerability in detail.
Great Service for White Hats
With Spyse, security engineers and system administrators are placed a step ahead of cybercriminals. Being able to find loopholes and patch vulnerabilities at this pace can easily prevent leaks of sensitive data for businesses, employees, and partners. Spyse’s search engine is relatively straightforward in its use so that security personnel can implement it without going through long cybersecurity training programs.
Bug bounty hunters and penetration testers also receive great benefits from using this service. Spyse can economize time and money spent on developing its own infrastructure and can help avoid rate limits as well as stay invisible while performing mock attacks. Spyse can also be utilized when other methods are forbidden by bug bounty agreements.
Using this search engine can vastly improve the security levels of any infrastructure by giving specialists quick access to all elements exposed to the internet. This can help identify loopholes, patch vulnerabilities, establish protection systems and dramatically accelerate the process of safeguarding a network against hacker threats.