What is hacking
Hacking is a term that is often associated with criminal activity, and with good reason. The past 10 years are riddled with stories of notorious hacking incidents that shook the business world and almost brought many companies to their knees. The people behind malicious hacking exploits prey on weaknesses in the digital systems and networks of companies and once they gain entry, they commit crimes such as
• Steal information, mostly with the intention to expose or ransom it for money
• Block communication 7
• Upset business
But there are also hackers who penetrate systems just for fun, or for security testing. This differentiation of intention is what led hacking to be seen as a potentially good thing. The motivation or the intention behind hacking is what sets apart different types of hackers.
Black hat hackers. These are bad hackers. Their aims are malicious.
White hat hackers. These are the good guys. They are also known as ethical hackers. Their main aim is to stop black-hat hacking. Their activities are legal and are often carried out with the knowledge of the system or network owner. Most of them have ethical hacking certification, which enables them to work for governments and organizations.

Grey hat hackers. They hack for fun, often gaining entry into systems and networks without permission. But unlike black hat hackers, they don’t cause harm to the organizations or individuals they hack. They usually inform the owners of the security weakness discovered and may ask for a fee for their efforts.
More about Ethical hacking
As mentioned, ethical hacking is legal and is done with a company’s authorization. Ethical hacking is also known as penetration testing as its main purpose is to “intrude” a system to discover any threats. Ethical hackers anticipate the actions of black hat hackers and even use black hat techniques to try to break into systems. If they discover any security loophole, they report it to the system owners and recommend solutions.
Why ethical hacking
Ethical hacking serves the following purpose:
• To recover data, such as corrupted files and lost passwords
• Penetration testing, done to assess the strength of network security systems
• As a continuous effort to develop stronger systems that are attack-proof
Skills of an ethical hacker
Ethical hacking requires certain key skills and hacking techniques. They include:
• Cracking passwords
• Session spoofing and jacking
• Network sniffing
• Creating viruses, trojan horses, worms and backdoors
• Identifying the denial of service (DoS) attacks. More importantly, be able to diagnose a system that has a combination of symptoms for such an attack. For example, network equipment that is improperly configured.
• Understand buffer overflows, what causes them, the risk they pose and how they can be exploited
• Understand databases and attack methods such as SQL injection, that can be used to attack data resources
• Cryptography
• Evading firewalls
• Cloud computing
• Expertise in computer systems and networks
• Programming
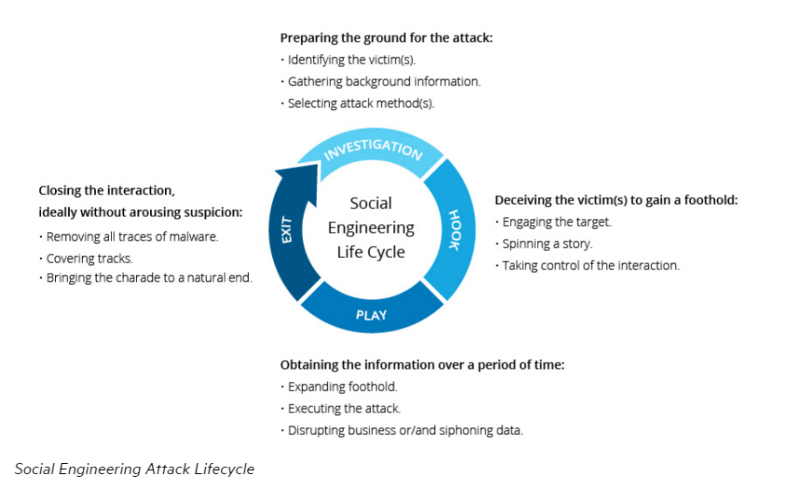
• Understand social engineering, both from an attacker and a victim mindset. Some cyber attacks rely on preying on humans as opposed to system vulnerability. Social engineering attack methods include scareware, phishing and pretexting.
It also helps to have these personality traits:
Patience. Black hat hackers can take years planning an attack. Patience and perseverance will help you to deal with big attacks when they happen.
Problem-solving skills. You will encounter challenges that seem impossible to solve. You will be required to solve them under pressure. Composure under pressure will come in handy when solving problems.
Black-hat hackers spend a lot of time perfecting their skills. As an ethical hacker, you can only outsmart black hatters by keeping your skills sharp. For this, you need to put in a lot of effort to learn not just the technical or science part of computer hacking, but also the art of it. In addition, stay up to date with the latest hacking technologies and techniques.
Map your Ethical hacking career path
The road to a successful ethical hacking career is exciting and challenging. But if you stick with it, you will have a rewarding career. To excel as an ethical hacker, proceed as follows:
1. Start by understanding computer hardware and software. You can study computer science or get A+ certification.
2. Get a job as a programmer or tech support.
3. Understand networks. Work as a system administrator or network engineer for some years. Relevant certifications in this area include:
• Networking: Network+, CCNA
• Security: Security+, Certified Information Systems Security Professional (CISSP)
Click here to learn more about the Introduction To CISSP By Chuck Easttom
4. Focus on gaining work experience. Continue reading everything about systems and networks. More importantly, engage your curiosity and experiment. As well, keep up to date with trends in anything to do with computers.
5. Enroll in an ethical hacking course. By the end of your course, you should have the skills discussed above.
6. Sit for exams and become a Certified Ethical Hacker (CEH) Certification.
Click here to learn about Certified Ethical Hacking V9 Certification Training Course
You should shape your career path to suit your current life and work circumstances. If you are already working in a different profession (for instance, as a data analyst), enrolling for a 4-year bachelor’s degree may not be the most practical option for you. On the other hand, a comprehensive online training program may be what you need.
About the ethical hacking certification
The Ethical hacking certification is a credential given to network security professionals trained and qualified in thwarting malicious attacks on computer systems and networks. The International Council of E-Commerce Consultants (EC-Council) is the sponsoring body behind the ethical hacking certification. The organization oversees training and certification of ethical hackers and also maintains standards for the profession. The EC-council also screens applicants to root out malicious hackers.
Companies and governments have been using hackers since before this certification were introduced. Its introduction was a necessity to regulate anyone with hacking skills and to ensure they adhere to a professional code.
You need at least two years of experience in a security-related role for the EC-council to consider you for the ethical hacking certification examination. If you don’t have the relevant work experience, you should first start by getting the relevant training mentioned above.
Only sit for the exam after you completed the certified ethical hacking course.
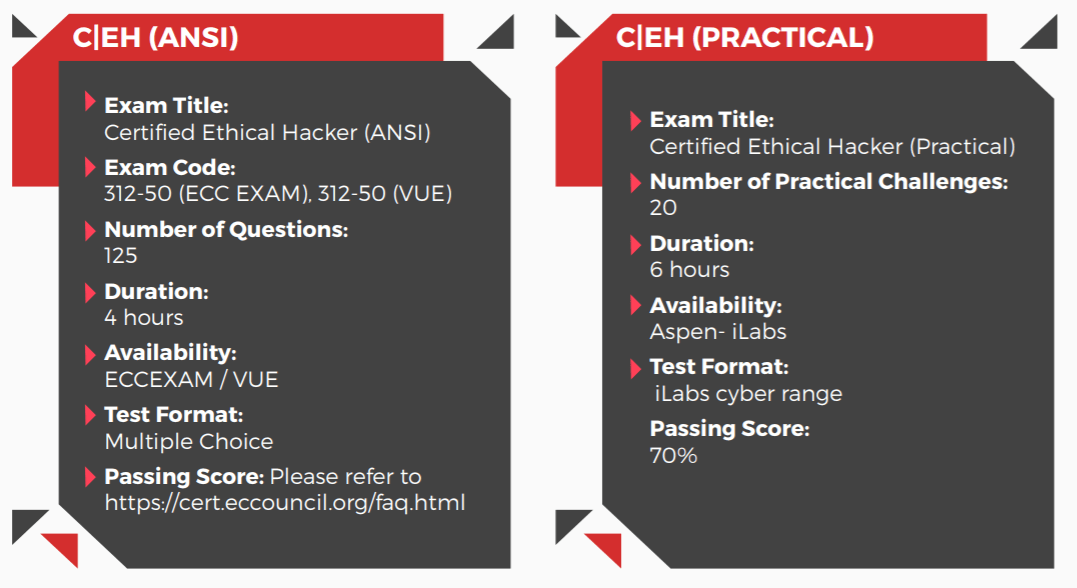
The exam has 125 questions and 20 practical challenges, all lasting a total of 10 hours. The exam is based on all the modules learned in the course. Note that the exam fee changes yearly.
Job Outlook
Cybersecurity is one of the fastest growing sectors, thanks to increasing instances of hacking and the need for organizations to protect themselves against these attacks. According to data from the United States Bureau of Labor Statistics, IT security jobs will grow by up to 28% until 2026.
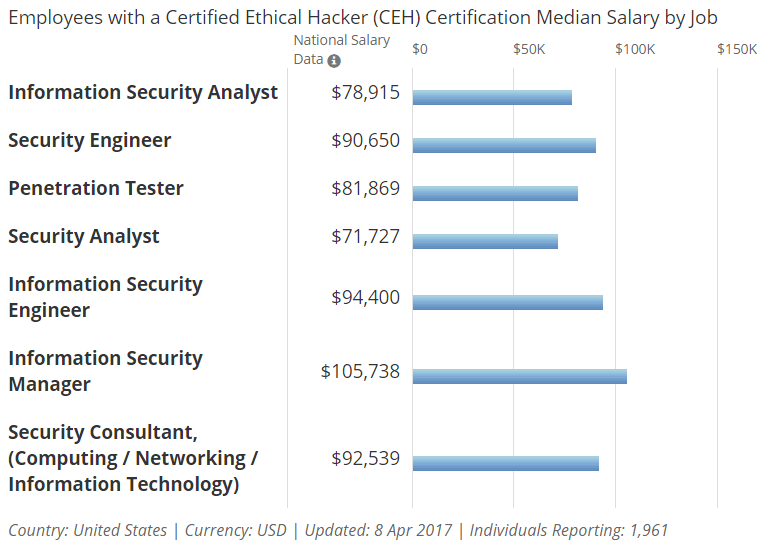
Overall, expect your job as an ethical hacker to be full of challenges but also extremely satisfying. Employers such as Fortune 500 companies and government agencies will push your thinking and performance in order to make their products and data safe. Expect to be well compensated for your skills; salaries range from an average of $77k for an information security analyst to $91k for a security engineer. Some companies even pay as high as $150k.
Final Note
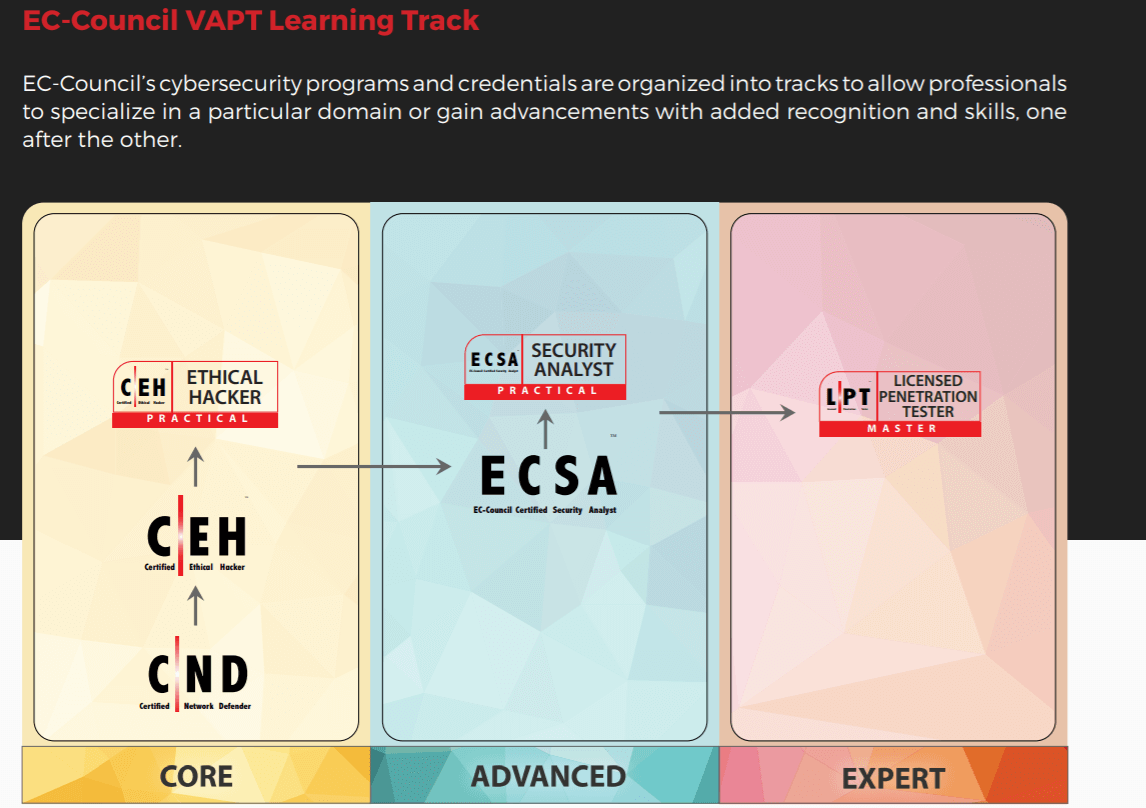
That’s it; the best way to map your career as an ethical hacker. Your journey doesn’t end with the certificate of ethical hacking. After you accumulate enough experience as a beginner ethical hacker, enroll for additional training, then apply to the EC-Council for advanced and expert level certifications.
That said, it’s important to remember that ethical hackers work within set rules. As you gain more expertise, respect your profession and follow the rules even when not at work.